Why Active Directory isn’t a defense strategy
Active Directory (AD) is a business enablement tool, not a security tool. It manages all authentication within the on-prem environment, deciding whether users can access requested resources. In theory, that should make AD the frontline defense against the malicious authentications that drive lateral movement.
In reality, it’s not. AD performs just one security check: whether the username and password match. That’s it. As a result, it can’t distinguish between legitimate use and compromised credentials. This is a critical blind spot, since lateral movement attacks rely on valid, stolen credentials to enable attackers to move undetected across systems.
Moreover, AD’s legacy authentication protocols and the tools that use them, like PsExec and Remote PowerShell don’t natively support Multi-Factor Authentication (MFA). Without MFA, there’s no way to verify whether a user is genuine or an attacker posing as legitimate.
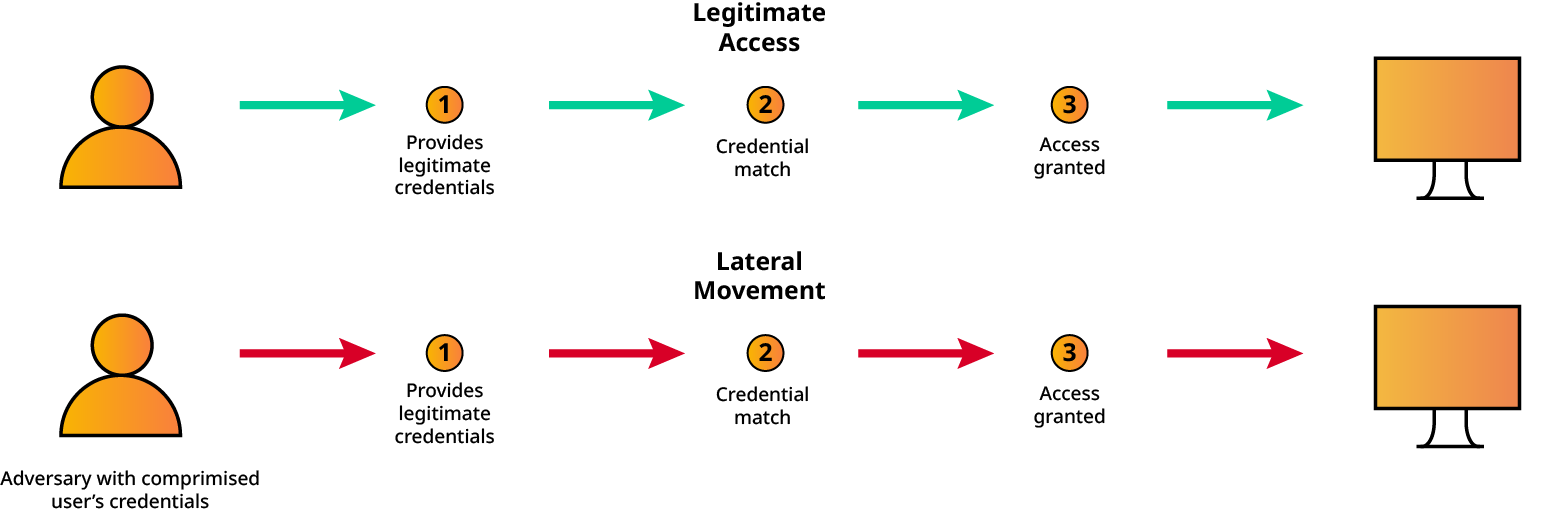
AD sees lateral movement as legitimate authentication, so it cannot prevent it.

Preventing Lateral Movement in Active Directory

AD sees lateral movement as legitimate authentication, so it cannot prevent it.
Active Directory (AD) is a business enablement tool, not a security tool. It manages all authentication within the on-prem environment, deciding whether users can access requested resources. In theory, that should make AD the frontline defense against the malicious authentications that drive lateral movement.
In reality, it’s not. AD performs just one security check: whether the username and password match. That’s it. As a result, it can’t distinguish between legitimate use and compromised credentials. This is a critical blind spot, since lateral movement attacks rely on valid, stolen credentials to enable attackers to move undetected across systems.
Moreover, AD’s legacy authentication protocols and the tools that use them, like PsExec and Remote PowerShell don’t natively support Multi-Factor Authentication (MFA). Without MFA, there’s no way to verify whether a user is genuine or an attacker posing as legitimate.

Preventing Lateral Movement in Active Directory

Why Active Directory isn’t a defense strategy