From a business standpoint, lateral movement can be the turning point in an attack. It often determines whether a minor incident stays contained or if it escalates into a major incident with detrimental financial, legal, and reputational consequences.
In the examples above, you’ll see two common types of lateral movement that align with techniques in the MITRE ATT&CK Framework. For a full list of enterprise-level lateral movement techniques, visit the MITRE website.
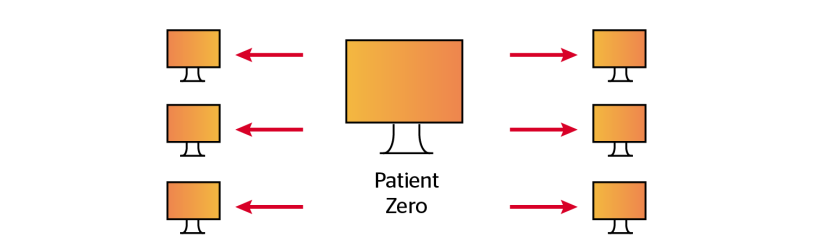
Ransomware: MITRE TA0040
Adversary profile: From cyber crime organizations to low-skilled threat actors
Target profile: Every organization regardless of size and vertical
Purpose: Encrypt victim’s machines to extort ransom payment in exchange for restored data
Lateral movement’s role: Gain the ability to plant and execute ransomware payloads on as many machines as possible
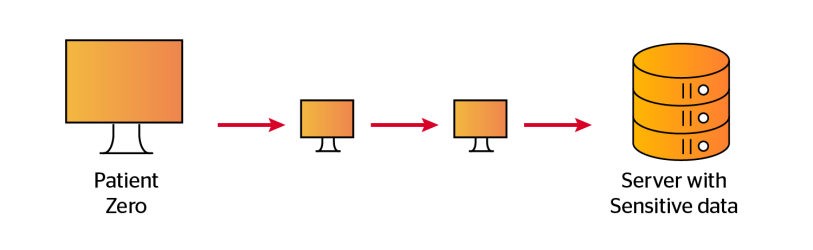
Data Theft: MITRE TA0010
Adversary profile: Elite groups of either nation states/cyber crime organizations
Target profile: Large enterprises and nation states
Purpose: Theft of sensitive information such as intellectual property, Personal Identifiable Information (PII), and credit card data
Lateral movement’s role: Gain access to the servers or applications where this information is stored

Preventing Lateral Movement in Active Directory

Operational impact:
From a local threat to an organizational-level incident
Preventing Lateral Movement in Active Directory


Ransomware: MITRE TA0040
Adversary profile: From cyber crime organizations to low-skilled threat actors
Target profile: Every organization regardless of size and vertical
Purpose: Encrypt victim’s machines to extort ransom payment in exchange for restored data
Lateral movement’s role: Gain the ability to plant and execute ransomware payloads on as many machines as possible
Data Theft: MITRE TA0010
Adversary profile: Elite groups of either nation states/cyber crime organizations
Target profile: Large enterprises and nation states
Purpose: Theft of sensitive information such as intellectual property, Personal Identifiable Information (PII), and credit card data
Lateral movement’s role: Gain access to the servers or applications where this information is stored
From a business standpoint, lateral movement can be the turning point in an attack. It often determines whether a minor incident stays contained or if it escalates into a major incident with detrimental financial, legal, and reputational consequences.
In the examples above, you’ll see two common types of lateral movement that align with techniques in the MITRE ATT&CK Framework. For a full list of enterprise-level lateral movement techniques, visit the MITRE website.
Operational impact:
From a local threat to an organizational-level incident