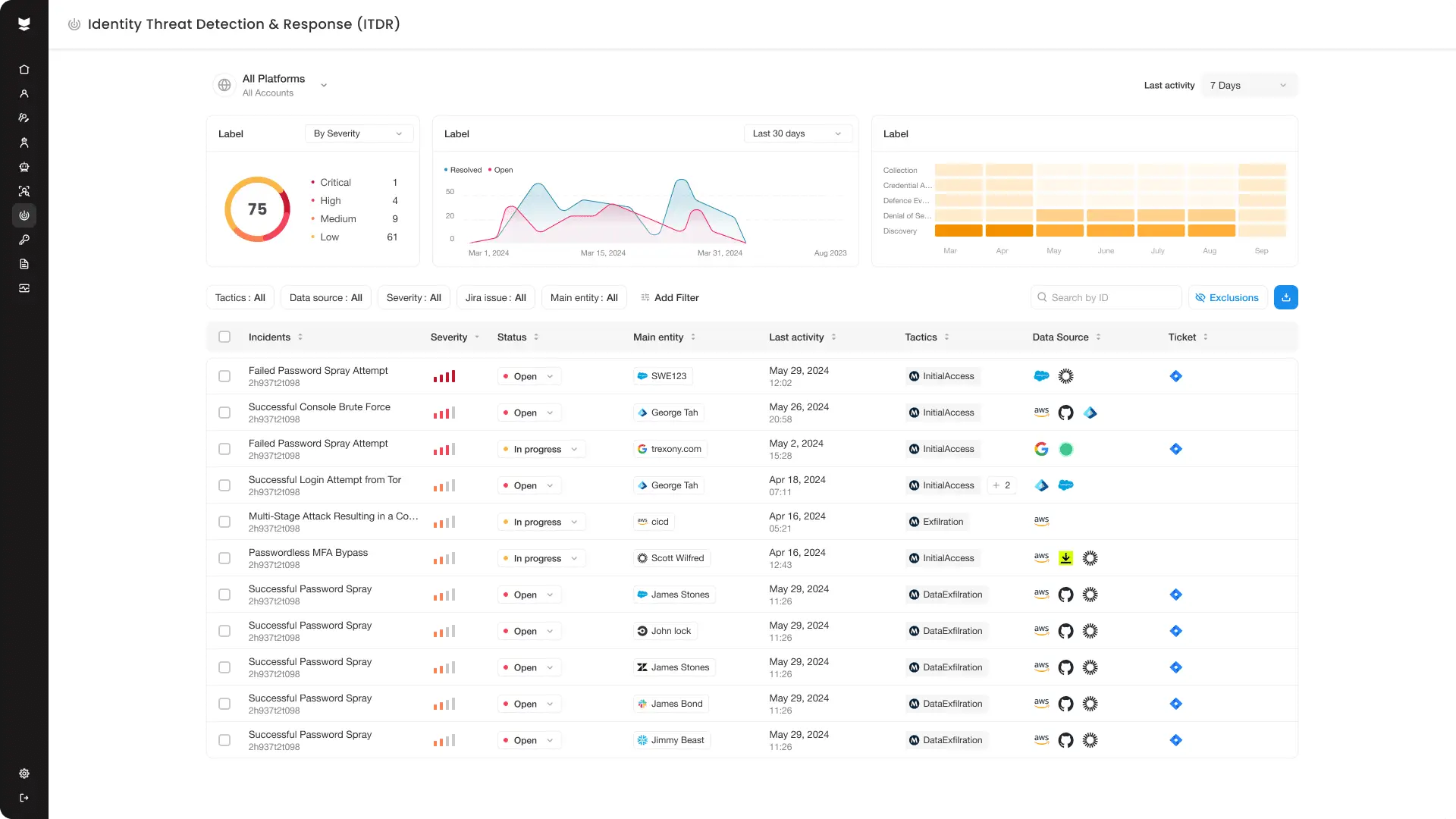
The 4 Silverfort ITDR pillars
1. Monitor all access attempts
AD (and all other IdPs in the environment) forward every incoming access request to Silverfort, awaiting its verdict on whether to grant access or deny it. This vouches for 100% coverage of all access attempts.
2. Identify anomalous activity
Silverfort’s risk engines continuously scan for
malicious authentication protocol modifications (like Pass-the-Ticket, Pass–the-Hash and others)as well as for user access anomalies including the source and destination machines that the user accesses, the volume of initiated access attempts, and any other deviation from standard authentication.
3. Verify with MFA
Once an authentication is flagged as suspicious, Silverfort challenges the requesting user with MFA. The MFA would reveal in certainty whether the access attempt was indeed initiated not by the user but by an adversary with this user’s credentials.
4. Block malicious access
If the user denies the MFA challenge (or if it is a non-human identity such as a service account that clearly deviates from its baseline behavior), Silverfort instructs AD to block the the user’s access, blocking the attack in real time.

Preventing Lateral Movement in Active Directory

4. Block malicious access
If the user denies the MFA challenge (or if it is a non-human identity such as a service account that clearly deviates from its baseline behavior), Silverfort instructs AD to block the the user’s access, blocking the attack in real time.

Preventing Lateral Movement in Active Directory

3. Verify with MFA
Once an authentication is flagged as suspicious, Silverfort challenges the requesting user with MFA. The MFA would reveal in certainty whether the access attempt was indeed initiated not by the user but by an adversary with this user’s credentials.
2. Identify anomalous activity
Silverfort’s risk engines continuously scan for
malicious authentication protocol modifications (like Pass-the-Ticket, Pass–the-Hash and others)as well as for user access anomalies including the source and destination machines that the user accesses, the volume of initiated access attempts, and any other deviation from standard authentication.
1. Monitor all access attempts
AD (and all other IdPs in the environment) forward every incoming access request to Silverfort, awaiting its verdict on whether to grant access or deny it. This vouches for 100% coverage of all access attempts.
The 4 Silverfort ITDR pillars